Introduction
In response to these emerging challenges, Bangladesh Bank introduced the Cybersecurity Framework Version 1.0 in February 2025. This is a landmark development for Bangladesh. More than a regulatory document, it is a foundational framework that sets a minimum baseline for cybersecurity governance and controls across the financial sector.
Its significance extends beyond banks and payment institutions. It is also an important step toward building the capabilities needed for a secure and resilient information society in Bangladesh.
Why This Framework Matters
This Bangladesh Bank Cybersecurity Framework document is a seminal contribution to the cyber security landscape in Bangladesh. No such document was ever formulated. This is a foundational document for Cyber and will help creation of capabilities in the information society well beyond the financial sectors.
Bangladesh’s financial sector is rapidly transforming through digital services, online banking, payment systems, mobile financial services, and cloud-enabled platforms.
While this transformation improves customer experience and operational efficiency, it also increases:
- Cyber threat exposure
- Attack surfaces
- Technology dependencies
- Risks to customer data and financial stability
To address these risks, Bangladesh Bank introduced the Cybersecurity Framework Version 1.0 in February 2025 as a baseline standard for banks and other regulated financial institutions which establishes a minimum baseline for cybersecurity governance and controls for banks, NBFIs, MFSPs, PSPs, PSOs, and other financial/payment service providers in Bangladesh based on control framework.
In order to protect banks, non-bank financial institutions, mobile financial service providers, and other payment service operators (collectively referred to as “The Organization”) from escalating cyber risks, the framework is intended to serve as a baseline of cybersecurity standards and procedures. It points out that whereas quick digital change has greatly enhanced financial services, it has also expanded the attack surface and raised technical vulnerabilities. In order to combat this, the framework incorporates national ICT policies, previous Bangladesh Bank recommendations, ISO 27001 standards, and the well-known NIST Cybersecurity Framework. It requires a plan centered on the following essential tasks: Establishing enterprise risk management, clearly defining responsibilities (such as designating a qualified Chief Information Security Officer, or CISO), and fostering responsibility all the way to the operations level are all examples of governance and preparation. This is a strong design choice for the financial sector because reporting, accountability, and regulator communication are critical in highly regulated environments.
The Cybersecurity strategy which is used at organization is explained below:
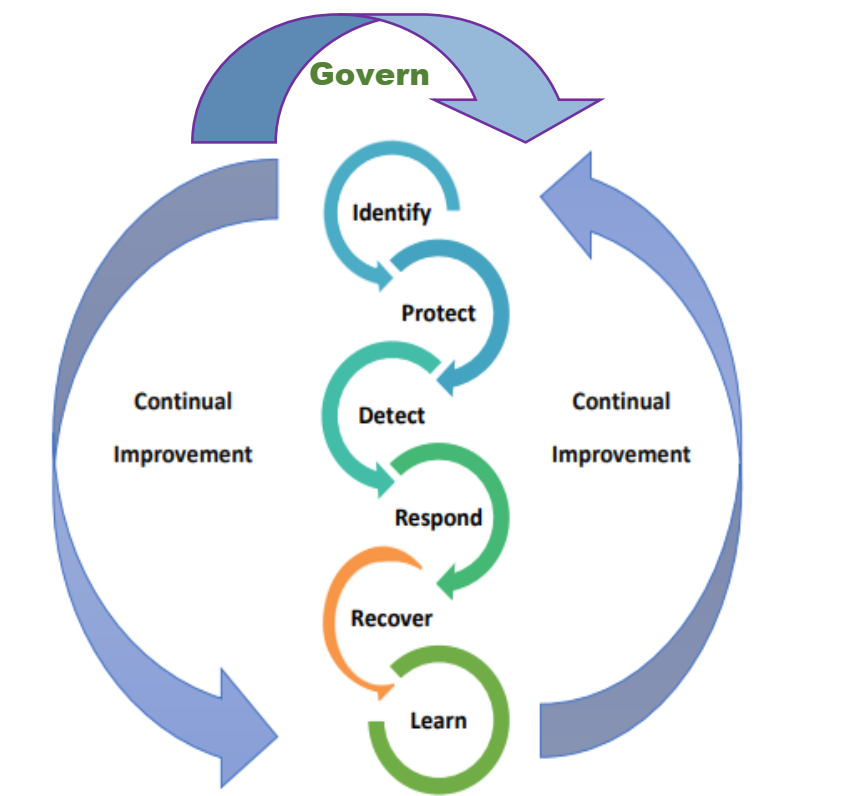
Fig: The Cybersecurity Strategy
Identify: Developing a thorough understanding of the organization context, asset management, risk management guidelines, and identifying risks from internal actors, cloud environments, and supply chains.
Protect: Putting in place robust measures to limit the effects of cyber incidents. This includes network integrity, data encryption, and identity and access management (such as Multi-Factor Authentication).
Detect: Implementing continuous monitoring systems to quickly identify network events, anomalies, and illegal active discovery tools.
Respond: When breaches happen, respond by developing strict incident response plans, establishing communication guidelines, and putting containment or mitigation plans into action.
Recover & Report: Following an event, returning operations to normal, evaluating lessons learned through Post-event Reviews (PIRs), and following stringent internal and regulatory reporting guidelines.
The Most Important Creation of Capabilities in the Information Society
This framework requires the development of highly specialized, critical capacities in the context of an emerging “information society” (where the production, dissemination, and manipulation of information is the most important economic and cultural activity). The most significant capability creations in the framework are:
- A proactive approach to cyber resilience and strategy rather than just defenses. The framework notes that “an absolute shield against cyber threats does not exist” and highlights the importance of strategic planning as a key component of best practices. It increases the capacity to anticipate and isolate intricate, multi-layered digital threats before they compromise core systems by mandating that businesses actively map out supply chain and cloud vulnerabilities.
- Continuous Behavioral Monitoring and Advanced Threat Detection The architecture requires the development of active detection capabilities instead of passive firewalls. This comprises automated systems to monitor staff and third-party service providers’ baseline behavior in order to quickly identify anomalies, as well as active network discovery technologies that should be used on a daily basis.
- Learning Capabilities (Formalized Post-Incident Intelligence) The structural shift from “surviving an attack” to “learning from an attack” is perhaps the most important skill for an evolving information society. Post-Incident Reviews (PIRs) and “Lesson-Learned” protocols are required by the framework. In order to ensure that the same error is never made again, this capability compels enterprises to identify the underlying causes, train staff on self-help, and constantly modify their security postures.
- Human Capital and “Cybersecurity Culture” Developing stakeholder awareness and “building a cybersecurity culture” are two of the framework’s main goals. It strengthens institutional muscle memory and elite human technical skill sets in the nation’s financial sector by requiring specific role training and creating Cyber Incident Response Teams (CIRTs) with clearly assigned leadership (e.g., Cyber Incident Management Coordinators).
The document’s greatest value is not just prescribing controls. The use of this document will help create trustworthy digital institutions, which are essential for the in the present world. Practical Takeaway. The most important capability it creates for the financial and information sector is a resilient, trusted, and skilled digital ecosystem capable of protecting data, maintaining critical services, and recovering from cyber incidents.